How Does Billions Network (BILL) Verify Identity? An Analysis of Its On-Chain Data Verification Mechanism
In today’s internet environment, identity verification has long depended on centralized platforms. User data is often stored in one place and submitted repeatedly, creating risks of privacy leaks and inefficient processes. Billions Network aims to address the core problems of data misuse and high trust costs through a mechanism that makes information verifiable without exposing it.
From the perspective of blockchain and digital assets, Billions is more than an identity tool. It is also a “trusted data layer.” It turns identity, behavior, and reputation into verifiable assets, allowing users, applications, and AI agents to build composable and scalable trust relationships.
Overview of the Billions Network (BILL) Identity Verification Mechanism
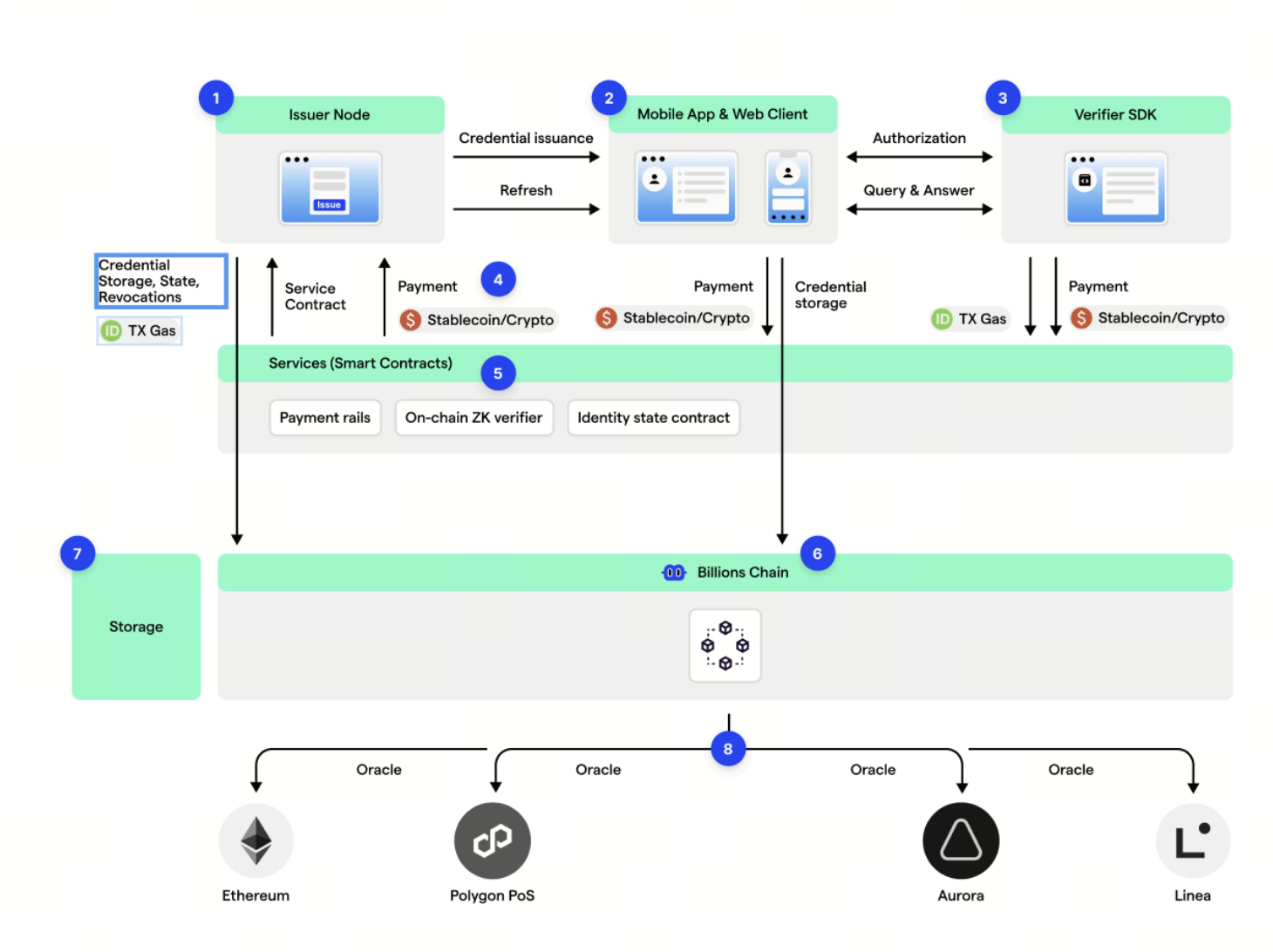
The identity verification mechanism of Billions Network (BILL) is built around the core principle of being verifiable without being exposed. It combines decentralized identity, DID, verifiable credentials, VC, and cryptographic proofs into a complete framework. Users control their own identity wallets within the system, using them to manage personal data and credentials instead of relying on centralized platforms to store information.
In practice, users first complete identity registration and verification through a mobile device, such as linking a social account, completing liveness detection, or submitting identity documents. This data is not made public directly. Instead, trusted issuers convert it into verifiable credentials that are stored on the user’s device. The entire process emphasizes local control and minimal disclosure.
The system follows the idea of “Onboard once, prove everywhere.” In other words, users only need to complete identity verification once, then reuse the result across different applications. This structure greatly reduces the cost of repeated authentication while improving the user experience.
From an architectural perspective, Billions is not merely an identity verification tool. It is a general purpose trust layer that connects applications, users, and AI agents through standardized verification interfaces, making identity a composable and reusable network resource.
Source: billions.network
How Billions Network Data Is Verified: Combining On-Chain and Off-Chain Data
In Billions Network, data verification uses a hybrid model of offchain generation and on-chain anchoring. Users’ raw data, such as identity information and behavioral records, is usually kept on local devices or in offchain systems to prevent sensitive information from being exposed.
When verification is needed, this data is converted into cryptographic proofs or verifiable credentials, then signed by an issuer to confirm its authenticity. For example, a KYC provider can issue a credential showing that a user has completed identity verification without revealing the user’s specific identity information.
The on-chain component is mainly used to record verification status and proof indexes, such as credential hashes and revocation status. This design keeps the system auditable while avoiding the cost and privacy issues that would come with putting large amounts of data on-chain.
This structure of offchain data and on-chain verification allows Billions to balance privacy protection with trustworthiness. It also provides a unified verification standard for use across different applications.
The Role of Zero Knowledge Proofs in BILL Identity Verification
Zero knowledge proof, or ZK proof, is a key technology in the Billions identity verification system. It enables users to prove an outcome without exposing the underlying data. For instance, a user can prove that they are over 18 without revealing their exact date of birth.
In the actual process, when a verifier makes a request, such as asking whether the user has passed KYC, the user’s device generates the corresponding cryptographic proof and sends it back to the verifier. The verifier only needs to check whether the proof is valid and does not need access to the raw data.
This mechanism not only strengthens privacy protection but also reduces the risk of data leaks. Even if the verification process is recorded, outside parties cannot reverse engineer the user’s real identity from it.
Zero knowledge proofs also support selective disclosure. This means users can provide different levels of information depending on the situation, giving them more flexible control over their identity.
How BILL Verification Data Is Accessed and Reused
One major feature of Billions Network is the reusability of verification results. After completing identity verification once, users can reuse the same credentials across multiple applications without submitting their data again.
This reuse is enabled through standardized interfaces, such as Verifier SDKs or on-chain verification contracts, allowing different applications to read verification results in a unified way. It is similar to OAuth login in Web2, but without relying on a centralized platform.
At the on-chain level, verification results can be called by smart contracts in the form of proofs and used for access control, airdrop filtering, governance voting, and other scenarios. At the offchain level, enterprise systems can also access verification results through APIs for compliance and risk control.
This ability for composable verification turns identity data from static information into a dynamic resource, helping the Web3 ecosystem move toward a more efficient model of data collaboration.
Security and Privacy Protection in Billions Network Identity Verification
Billions Network is designed with security by default in mind, using multiple layers of mechanisms to protect the reliability of its identity system. First, data is generated and stored locally on the user’s device, avoiding the leakage risks associated with centralized databases.
Second, the system uses an unlinkability design. Different applications see different DID identifiers, so they cannot connect a user’s behavior across platforms. This effectively helps prevent privacy tracking.
In its security model, the network reduces single points of failure through multiple issuers, key rotation, and revocation systems. Once a credential is revoked, the related proof becomes invalid immediately, without exposing the user’s identity.
The system also introduces Sybil resistance mechanisms, such as uniqueness verification and reputation scoring, to prevent fake identities from abusing network resources and to protect the trustworthiness of the broader ecosystem.
Advantages and Potential Limitations of the BILL Identity Mechanism
The first major advantage of Billions Network is the way it combines privacy with verifiability. Users can complete identity verification without exposing sensitive information, which is especially valuable in financial and AI-related scenarios.
Second, its ability to reuse verification results across platforms significantly reduces authentication costs and turns identity into a transferable “trust asset.” This structure helps support a unified digital identity infrastructure.
However, the mechanism also has certain limitations. For example, the system depends on the quality of issuers. If the credential source is unreliable, the overall level of trust will be affected. In addition, complex cryptographic processes may raise the barrier for users to understand and use the system.
At the regulatory level, decentralized identity still needs to find a workable fit with traditional compliance systems. How to balance privacy protection with regulatory requirements remains a long term challenge for this type of system.
Conclusion
Billions Network (BILL) combines DID, verifiable credentials, and zero knowledge proofs to build an identity verification system centered on privacy protection. Its core innovation is shifting identity verification from data sharing to result proving, creating a safer way to support data interactions.
This mechanism not only gives users greater control over their data, but also provides scalable trust infrastructure for the Web3 and AI era. As demand for digital identity continues to grow, models like this may become an important part of the future internet.
FAQs
What is the core feature of the BILL identity verification mechanism?
Its core feature is proving rather than disclosing. Users can complete identity verification without exposing their raw data.
How does Billions Network protect user privacy?
It minimizes data exposure through local data storage, zero knowledge proofs, and unlinkable DID design.
What role do zero knowledge proofs play in the system?
They are used to prove that a certain fact is true without providing the specific underlying data, such as proving age or identity status.
Can verification results be used across platforms?
Yes. Users only need to complete verification once, then reuse the result across multiple applications.
Is Billions Network fully decentralized?
Its identity control is decentralized, but it still relies on issuers and verification nodes to jointly maintain the trust system.
Related Articles

The Future of Cross-Chain Bridges: Full-Chain Interoperability Becomes Inevitable, Liquidity Bridges Will Decline

Solana Need L2s And Appchains?

Sui: How are users leveraging its speed, security, & scalability?

Navigating the Zero Knowledge Landscape

What is Tronscan and How Can You Use it in 2025?


